Hacker vulnerability in modern vehicles raises questions for OEMs, insurers, body shops
By onEducation | Repair Operations | Technology
The lack of security for connected cars — particularly from OBD ports — poses a huge threat to drivers as vehicles become more complex, experts said last month.
Dongles — OBD-II plugins such as those mailed to users by insurers — are “an enormous threat vector,” AutoImmune founder Karl Heimer said during an Automotive World cybersecurity webinar. (See slides here.)
With physical access to a vehicle, “I can do pretty much anything I want,” Heimer said.
Wired reported in August that scientists from the University of California, San Diego used a Metromile Pulse “dongle” — a device which plugs into an OBD-II port — made by Mobile Devices to hack a Corvette.
Besides attacks on the dongles themselves — made even easier by those which still use unsecured public wireless networks to communicate — there’s the tremendous threat poised by plugging something you got in the mail into a computer terminal, according to Heimer.
More RDN security coverage
- Expert: Hackers could turn dealership, collision repairer into ‘auto brothel’
- Credit card fraud/theft liability soon shifts to merchants — like body shops — who swipe stripe instead of chip
He referenced the security breaches which can occur through the “thumb drive in a parking lot” cybersecurity scenario, in which an employee plugs a USB stick found outside into a workplace computer. A program loads from the drive, and voila, the entire office network has a virus or has unknowingly granted a hacker administrator privileges.
Hackers could time a phony mailing with a recall, he said, urging users to plug a fake patch device into the port.
The OBD-II port attacks rely on someone to actually plug the tainted object into the car. The infamous hack of a Jeep Cherokee this summer with a Wired reporter inside did so simply by breaking into the uConnect system. With cars more connected on various networks and offering more and more features already hackable on personal computers and smartphones, OEMs have reason to worry.
Besides the drama of such an attack, it seems that security steps taken — or not taken — by OEMs might have some impact on repair operations. For example, new equipment necessary to use a more secured OBD port or the possibility of a “car virus” somehow being transmitted to your system.
OEMs have also sought to restrict access to vehicle electronics through the Digital Millenium Copyright Act, citing security and environmental grounds. (See this April Autoblog piece for an deeper look at the issue.)
While the proposal was likely intended to target aftermarket manufacturers or modders rather than collision repairers — automakers are busy building networks of certified repairers which rely on independent shops — it still highlights an OEM argument for changing who can work on a car.
In any case, the issue is alarming — and fascinating — enough to merit attention from professionals who work on cars for their jobs and drive them as consumers.
Complexity and security
The sheer complexity of an automobile “operating system” makes security difficult. As has been famously observed in the past, a car has more lines of code than the space shuttle.
Estimates presented by Black Duck put a connected car at 150 million lines of code and a self-driving car at 300 million lines of code (at a minimum); for comparison, the Android cellphone core OS only has 12 million lines of code.
“This much code means it’s harder to write, to manage, to control quality, and consequently, to secure,” Black Duck open source strategy Senior Director Bill Weinberg said.
These difficulties rise exponentially, further complicating automotive cybersecurity efforts.
“We don’t even know the extent of the problem,” Weinberg said, and he said even OEMs and other suppliers aren’t even able to determine it.
All industries have been very proprietary in the past with their software, but have been incorporating more and more open source code (publicly available, free to use and modify). In fact, Weinberg said some of Black Duck’s customers don’t even realize they’ve used open source.
Learn more about OEMs at SEMA Repairer Driven Education
Those wanting to learn more about what the automakers will be throwing at your shop in the future should attend the special OEM Collision Repair Technology Summit at the SEMA Show as part of the Society of Collision Repair Specialists’ Repairer Driven Education Series. The sessions include “Advanced Automotive Technology,” “The Future of Aluminum in the Automotive Industry” and “The Continuing Evolution of Advanced Steels in Automotive Bodies.” There’ll be a heavy emphasis on joining, lightweight materials and the scans necessary to make sure all the new tech works. Register here.
Open source and proprietary systems
The presentation indicated both types of code would be a factor as cars evolve. Both have security benefits and flaws, and the debate over which is more secure is “an eternal question,” Weinberg said.
With a proprietary system, it’s harder for a hacker to plan an attack. However, it also requires taking a great deal on faith from the OEM. (“We can’t show you the proof, but trust us, this is safe from hackers.”)
“I would really have to have a great deal of assurances,” NVIDIA Chief Security Architect Hadi Nahari said of a proprietary system.
With open source, the guts are totally exposed — but the added oversight can actually make for a better product.
“There’s many many people beating on the code,” Green Hill Software ISS Business Unit Vice President and General Manager David Sequino said, and Nahari likened it to kicking car tires at a dealership.
“Risk absolutely is proportional to code size,” Heimer said.
OEMs taking notice
OEMs must also get the supply chain in order, Sequino said. Ultimately, they’re on the hook for a problem even if the issue really lies with a Tier 1 company which supplied the hackable device.
“The OEM owns the problem,” he said.
Automakers had brushed off the issue even a year or two ago, relegating digital security “second-class citizen” status, according to Nahari.
However, they’re beginning to pay attention (the high-profile hacks probably didn’t hurt), and NVIDIA has been getting more inquiries, he said.
“This is all promising,” Nahari said. However, he said he still didn’t see “good comprehension” yet on the depth or scale of the problem.
That’s a problem, he said. A breached computer might lose data, which is inconvenient. But a breached car is far more serious.
“There’re lives attached to these devices,” he said.
More information:
“Webinar: A sideways glance at the automotive security threat landscape”
Automotive World, Sept. 24, 2015
Images:
A Metromile OBD-II plugin is shown here. Wired reported in August that scientists used the dongle made by Mobile Devices to hack a Corvette. (Provided by Metromile)
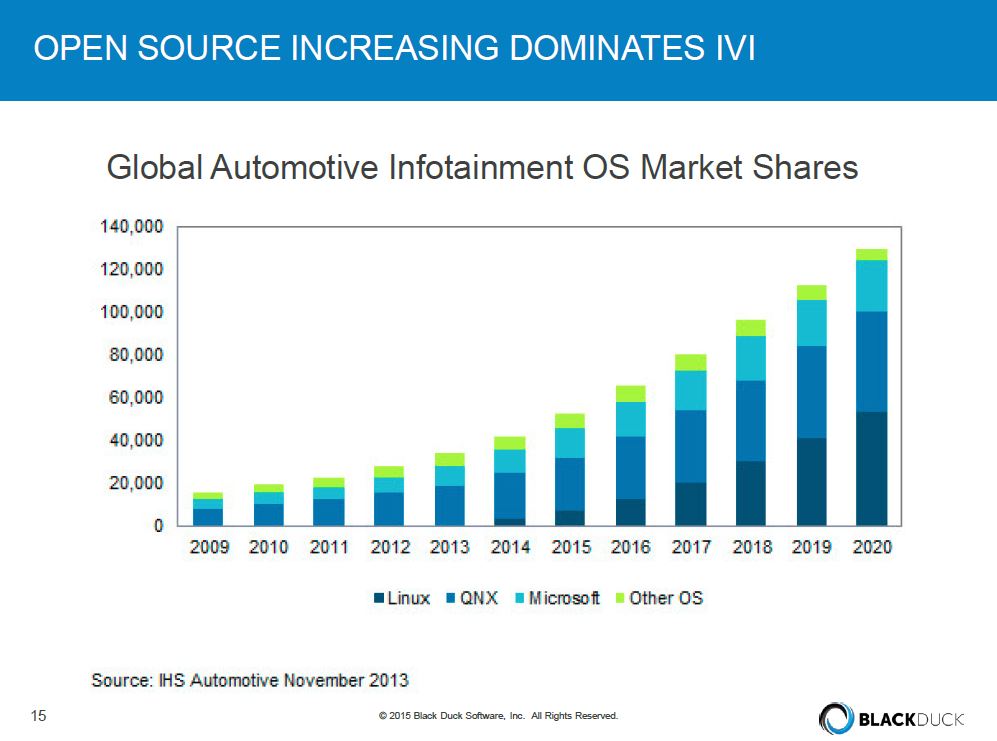
Open source code drives a great deal of in-vehicle infotainment (IVI) systems. (Provided by Black Duck via Automotive World webinar.)