Anderson calls ransomware ‘real issue in our industry’; insurer shares cyber risk coverage tips
By onAnnouncements | Associations | Business Practices | Education | Legal | Market Trends | Technology
Collision Advice CEO Mike Anderson on Monday said he had firsthand knowledge of more than a dozen auto body shops which have suffered a ransomware attack — with all but one having to pay the extortionists.
“None of their IT people could get them out of it,” he told a Monday CIECAst. “… This is a real issue in our industry.”
Anderson said the largest ransom demanded neared $30,000. He said everyone he had talked to was able to negotiate the price down, however.
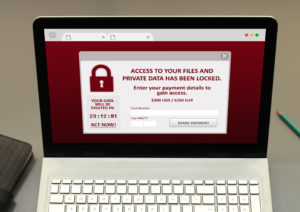
Ransomware attacks can bar access to one’s files and demand the victim pay to get them back. Failure to pay by a specific deadline might lead to the files lost forever. Anderson said all but one of the shops he knew of paid the hackers. The other one opted to rebuild their system — but “it took them several months,” according to Anderson.
Even the parent company of No. 2 national MSO Gerber Collision suffered a ransomware attack in 2019. Boyd Group Services said then “immediately implemented countermeasures” and had begun “back-up and recovery plans” to fix its systems.
David Willett, value creation executive at ProSight Specialty Insurance, said a new threat has arisen as cybercriminals realize companies are able to recreate their systems held hostage. (For example, using files backed up somewhere safe.) Hackers are now ransoming personally identifiable information which they’ve harvested from victim systems as well.
“Now they’re holding both,” he said.
Willett said people will tell him they don’t collect personal information, to which he’d respond “‘You probably do.'” There’s probably someone in your organization storing it in the system simply because it’s more convenient, he said.
Willett said he first heard of collision repairers suffering ransomware attacks in 2016, followed by a “trickling” in 2017 and 2018.
He said that based upon insurance claims, the subset of the industry tied to dealerships have experienced such attacks for a longer time and more frequently. A study by dealership technology firm CDK Global found 24 percent of respondents hit by a cyberattack within the past two years, Willett said.
Willett said he’s seen “six-figure” ransoms, even an “outlier” seven-figure demand. He said negotiation is usually possible — they were able to negotiate the seven-figure ransom “substantially” — but the business’ cyber risk insurance might not cover the full amount.
Willett said policies might include a sublimit for ransomware, giving $10,000 and $20,000 as examples.
“I think that’s a light sublimit,” he said. The business will want to either raise the sublimit or remove the sublimit and set the extortion limit the same as one’s overall cyber risk liability, he said.
“This is what I see frequently,” he said, referring to companies with insufficient sublimits.
The presentation also highlighted the idea of having adequate PII theft coverage. Willett warned that a separate sublimit might exist there.
Willett said it’s possible one’s cyber risk insurance policy might also lack “extortion coverage.” If a shop lacks this specific protection, they likely aren’t covered for ransomware, he said.
Another concern would be exclusions tied to that extortion coverage, he said. They might state “you are not covered if you haven’t taken every precaution. Okay, well, what is ‘every precaution’?”
The better policies lack such exclusions, but the caveats still can be found today, according to Willett.
Anderson said he felt it was important businesses talk to their insurer ahead of any possible issue, for after the fact was “just too late.”
Willett said it’s been predicted that businesses in general will see more hacking following the 2020 U.S. election. Essentially, the cybercriminals currently trying to hack the election system will have more free time to bother businesses.
More information:
“CIECAST Oct 2020 Cybersecurity for the Collision Repair Industry”‘
Collision Industry Electronic Commerce Association YouTube channel, Oct. 26, 2020
CISA and Multi-State Information Sharing and Analysis Center, Sept. 30, 2020
Cybersecurity and Infrastructure Security Agency “Ransomware” webpage
Federal Trade Commission “Online Security” portal
CISA small and medium-size business cybersecurity information
FTC small business cybersecurity information
Featured image: A representation of ransomware. (glegorly/iStock)
